Unattended Access
When you are authorized to access the equipment remotely and/or when there is no on-site staff to establish the connection.

Secure Access. Round-the-Clock.
Experience seamless Unattended Access through the BifrostConnect Manager, utilizing default Multi-factor authentication and a mobile app for user identity verification—no on-site personnel required.
Step 1
Power on Bifrost Unit
Step 2
Connect to endpoint
Step 3
Authenticate with MFA
Opt for Unattended Access for continuous, secure authentication
Utilize Unattended Access to establish a secure, continuous connection, empowering your specialists to deliver seamless remote support without dependence on on-site personnel.Built for:
Yes, it's possible to remotely access offline equipment
Security policies increasingly prohibit online connectivity for operational technology to protect mission-critical equipment. But when disaster strikes at locations with no technical staff on-premises, troubleshooting or rebooting the system cannot be executed remotely. Your only option is to pack your bags and travel on-site. Or is it?
Unattended Access enables you to access your offline equipment remotely without relying on on-site personnel. Get instant hands on the faulty equipment and identify the core of the incident by analyzing the logfiles or entering the BIOS. If ever in doubt – try rebooting the system from the comfort of your chair.

Your Benefits

Reach beyond software

Reach beyond OS

Reach beyond config
Secure your IT/OT infrastructure
For IT security teams, human error is the ultimate foe. The perfect infrastructure is only as strong as its weakest link and when mission-critical technology fails, sending people on-site often introduces the conditions for the perfect storm. Suddenly offline equipment gets connected to the internet or unauthorized devices finds their way onto the company network – what should have been a temporary quick fix ends up as invisible rouge backdoors.
With Unattended Access, you can reduce the need for on-site visits by providing secure access to specific equipment without installing any software or entering the company network. Stay in control of User Rights and eliminate the need for rouge solutions in your infrastructure.
The results? Increased security and faster recovery times across your organization.
Your Benefits

Protect your network

Protect your devices

Protect your users
Expand the reach of your IT professionals
Scaling organizations is a tough job for modern leaders. Either you’re juggling with the constant lack of qualified talent or trying to solve the eternal budget puzzle. Sending support personnel on the road does not align with efficiency targets, CO2 quotes or the bottom-line.
With Unattended Access, you can reduce the need for on-site travel while increasing your valued expert’s freedom to solve their tasks from the comfort of their chair. You’ll expand your company’s market reach while saving valuable resources and prolonging the life of the technology across the organization.
The result? Satisfied customers, happy employees, and healthy profits.

Your Benefits

Optimize customer satisfaction

Optimize efficiency

Optimize resources
POPULAR FEATURES:
Manager
USB Disk Emulation
Shortcuts
Terminal Sessions
MFA or SAML
Relay Toggle
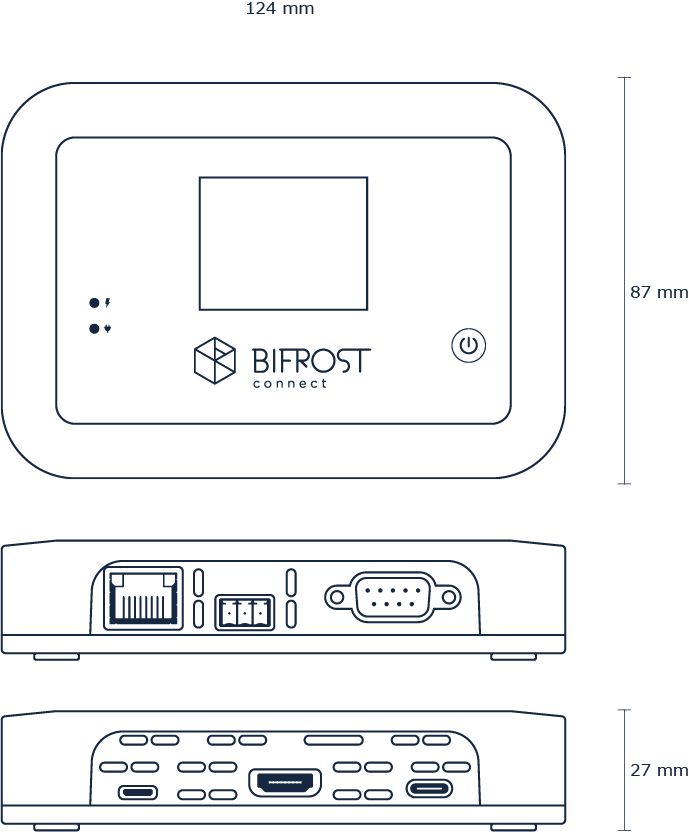
Technical Specifications
We know you love a good specsheet
Dimensions
Case size
L-124mm W-87mm H-27mm
Weight
250 g
LCD Display
2” TFT
General info
Data channel
Encrypted WebRTC via MQTT
OS
Industrial Linux with OTA updates
Humidity and temperature
Max. 85% non-condensing relative humidity
41 ̊-104 ̊F (5 ̊-40 ̊C)
Connectivity
Built-in LAN, WIFI, LTE (3G and 4G)
Input/Output
USB-C
Video input, keyboard/mouse output and charging
Bluetooth 4.0
Keyboard/mouse input
Micro-USB
Keyboard/mouse output and charging
Ethernet RJ45
Network (POE) and charging
RS232
Terminal session
SPDT
Power relay
HDMI
Video input up to 1080p @60Hz
SIM tray
Nano-SIM
Battery
Type
Industrial RRC1120 (1S1P)
Power
3.70V / 2,000mAh / 7.4Wh,
~2 hours battery operating time
