IP Tunnel
A Clientless Alternative to VPN
Create a Zero Trust network without VPN Tunneling or exposing any endpoints to the Internet.
Remote Access as it should be
Point-to-Point IP communication to critical infrastructure
Bifrost IP Tunnel is a secure way to access private endpoints and applications without a VPN or Remote Access Software. Our innovative approach is based on an adaptive trust model that grants access on a "need-to-know" basis, defined by granular policies. Combining hardware and Zero Trust principles, BifrostConnect adds an extra layer of protection to safeguard your highvalue assets.
User Experience
VPN:
Bifrost IP Tunnel:
Security
VPN:
Bifrost IP Tunnel:
Management
VPN:
Bifrost IP Tunnel:
Clientless IP Communication as it should be
Grant Endpoint Access
Minimize Attack Surfaces
Boost User Experience
Support IP Communication
Experience Zero Trust IP Access
Hasslefree Point-to-Point Access without extensive setup or expert knowledge.
Endpoint

On-site Staff
Prepare the endpoints for Remote Access by connecting the devices to the Bifrost Units via LAN.
The Bifrost Unit appears on the endpoint’s local network but does not interact.
MFA Interface
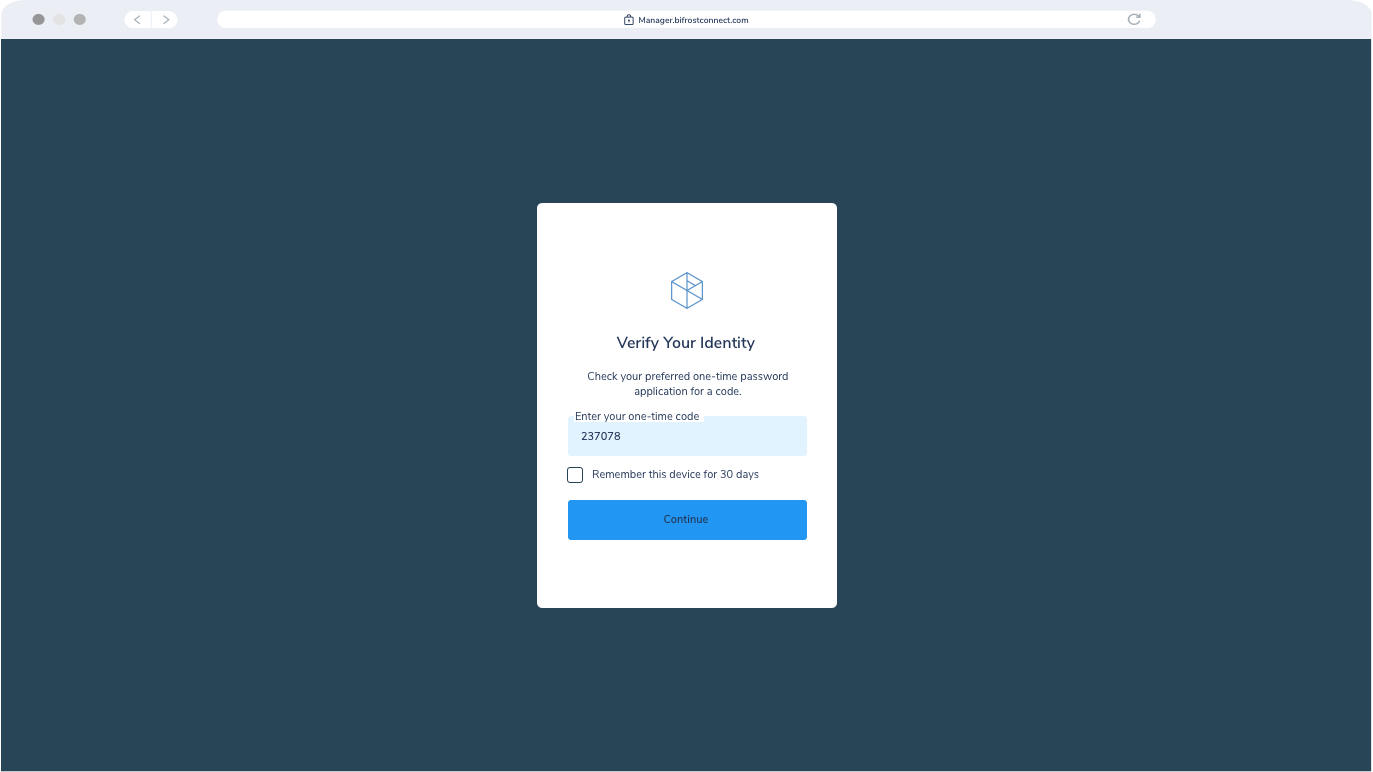
Admin or Privileged User
Authenticate via Multi-Factor Authentication (MFA).
The Authenticator service validates the User's right to enter the Interface or Manager.
The Authenticator service validates the Users’ right to access and configure the specific Bifrost Unit.
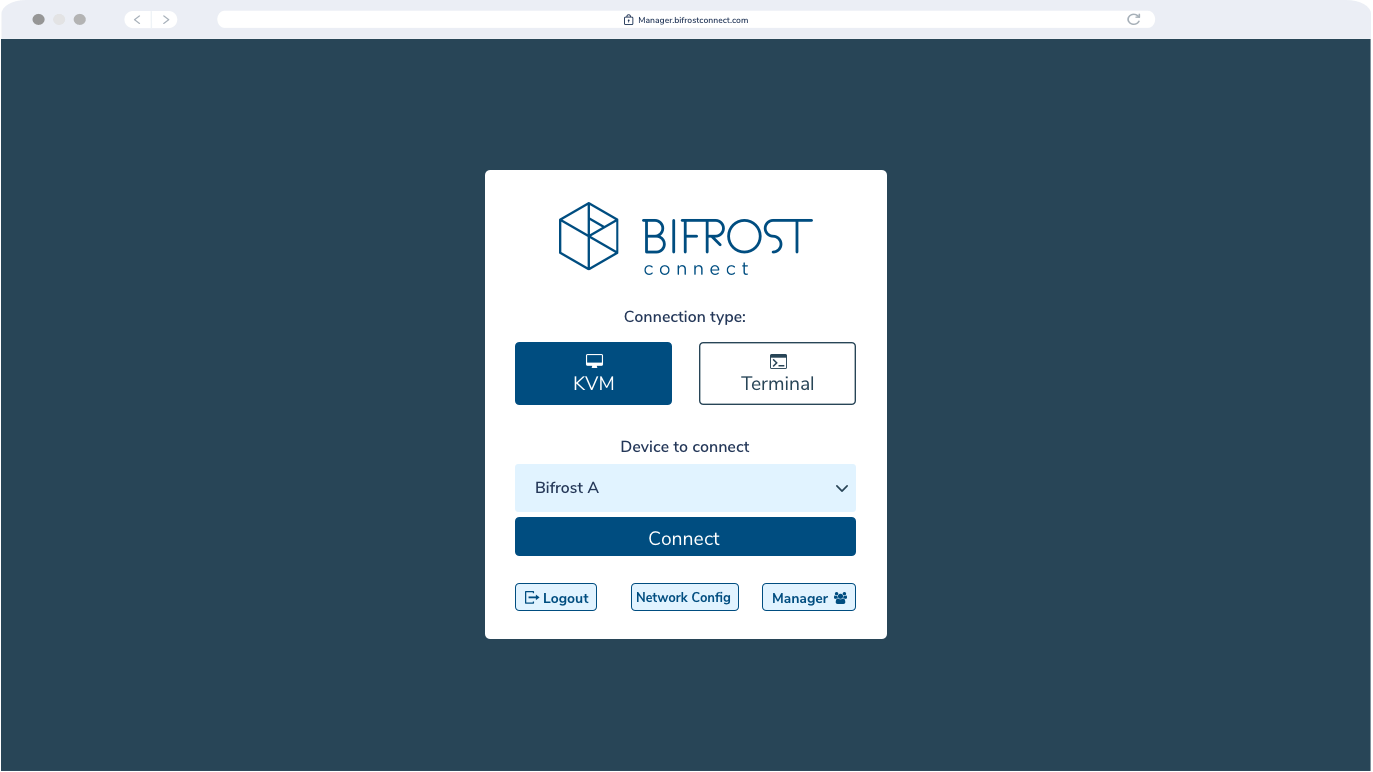
IP Tunnel Interface

Admin or Privileged User
Specify the IP addresses and ports enabled for remote Access during the session.
Endpoints connected to the Bifrost Units will be on a closed network and can communicate with the defined IPs and ports.

Privileged User or Remote Operator.
Use applications to communicate or transfer data through the local network.
Users with access to the destination endpoint have application access on IP and Port levels.
Session Terminated
On-site Staff or Privileged User
Terminate the session upon completion.
Optional: Disconnect the Bifrost Unit
If the Operator wishes to reconnect, a new session with valid authentication is required.
Discover How You Can Establish Zero Trust Access to Your Equipment
Get in touch with one of our experts today.
Empower privileged users with Just-in-time IP Tunnels
A Bifrost IP Tunnel enables a direct end-to-end encrypted connection between two Bifrost Units. These Point-to-Point tunnels are created on a per-session, on-demand basis, and all session data is transitory and will not be stored on any server.
Bifrost Units can utilize the Internet In-band or through the integrated Out-of-band connection. A Bifrost Unit does NOT share the Internet connection with the endpoints during an IP Tunnel Session. Advancing upon Least Privilege principles, IP Tunnel Sessions can only be initiated by Users or Admins with the required privileges. Additionally, privileged users must specify the IP addresses and ports enabled for remote Access during the session.
Combined with Bifrost KVM Access, privileged users can establish Remote Access without using software while configuring an IP Tunnel Session. This enables the privileged user and the Bifrost Units to be in three different locations during Remote Access.
How it works
Site A: Position the Bifrost Unit you wish to define as IP/Port forwarding Destination. Site B: Position the Bifrost Unit you wish to define as IP/Port forwarding Source.
As the Master/receiving end, Site A will always initiate the Pull or Push requests during sessions. This can be selected dynamically. When initiated and configured, endpoints connected to the Bifrost Units at Site A and Site B will be on a closed network and can communicate with the IPs and Ports defined by the privileged user. Other Users with Access to the device at Site A can now operate the equipment without requiring any vulnerable credentials that can be exploited after Session Termination. To maximize safety, equipment at both sites can be Offline, enabling Air-gapped Remote Access. If a user wants to access another private endpoint simultaneously or from another device, privileged users can spin up different IP Tunnels. When devices are offline or behind a firewall, inside-out connectivity masks the network from the internet while enabling application access to individual endpoints within the network.
Bifrost-to-Bifrost: IP Tunnel
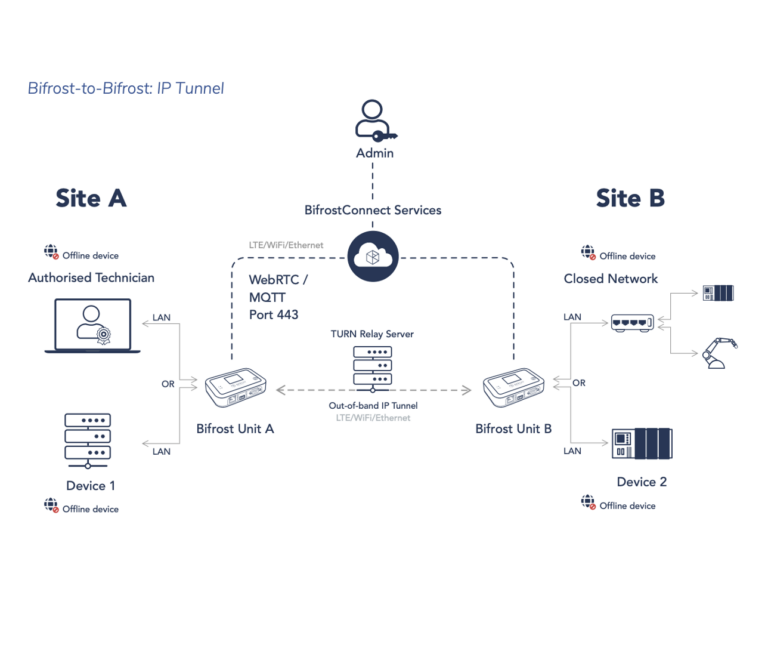
In the technical illustration, the Bifrost Unit at Site A is set up as the IP/Port forwarding destination. At Site B, the Bifrost Unit is set up as the IP/Port forwarding Source. As the master or receiving end, Site A initiates either Pull or Push requests during sessions. This selection can be adjusted dynamically.
Upon initiation and configuration, endpoints connected to the Bifrost Units at Site A and Site B form a closed network, allowing communication only with the IPs and Ports defined by the privileged user. By design, it is impossible to perform network scans of the endpoints through a Bifrost IP Tunnel.
Learn more about our security documentation on this page:
BifrostConnect Security Documentation
A Unified Remote Access Platform
Together as a suite, the BifrostConnect Solution gives you unmatched flexibility in tailoring your Zero Trust Access and scaling up your existing setup.
Secure
- Air-gapped Remote Access
- Out-of-band LTE connectivity
- End-to-End Encryption
- Transitory Session Data
- Multi-Factor Authentication
- SAML integration
- Access Management
- Audit Logging
Versatile
- Support all platforms
- IP Tunnel Sessions
- KVM Sessions
- Terminal/Serial Sessions
- SSH Sessions
- File Transfers
- BOOT/BIOS Access
- Portable/On-demand
Plug and Play
- Offline Remote access
- Hassle-free implementation
- No software installs
- No network configuration
- Out-of-the-box commissioning
- No on-site configuration
- Easy to use
- Hosted Private Infrastructure
Explore related resources
Is your organization equipped with the necessary tools to ensure your perimeter security remains intact during remote access?
How to take critical OT infrastructure offline while boosting remote access capabilities through air-gapped IP communication.
Zero Trust Access boosts remote work, expands market reach, saves resources, and prolongs technology lifespan.
Remote IP Communication
as it used to be
Conventional firewalls, VPNs, and Remote Access Software provide a considerable attack surface.
Externally exposed endpoints are vulnerable to cyber threats, allowing attackers to see and exploit them.
VPNs, in particular, can give attackers easy access to sensitive data by putting users directly on the network.
Traditional network security approaches often fail to prevent free lateral movement, leaving your network vulnerable to cyber attacks.
Legacy devices not designed with contemporary security standards are susceptible to cyber threats.
Connecting Legacy equipment to a VPN could inadvertently expose the entire network to attack.