WHERE VPNS END, BIFROST
CONNECT.
Introducing a new way of accessing equipment remotely.
With BifrostConnect Unified Out-of-band Access™ (UOA), we provide secure access to equipment that is offline, isolated, or not yet on the network. Commissioning teams, vendors, and operators can connect instantly – without waiting for VPNs, PAMs, or routed network paths to be in place.
No delays.
No dependencies.
Just secure remote access to critical assets, exactly when it’s needed.
We believe, that’s Remote Access, as it Should be..

CONNECT.
WHERE VPNS END, BIFROST
Introducing a new way of accessing equipment remotely.
With Unified Out-of-band Access™ (UOA), BifrostConnect provides secure access to equipment that is offline, isolated, or not yet on the network. Commissioning teams, vendors, and operators can connect instantly – without waiting for VPNs, PAMs, or routed network paths to be in place.
No delays.
No dependencies.
Just secure remote access to critical assets, exactly when it’s needed.
We believe, that’s Remote Access, as it Should be..

BifrostConnect's 5 Z approach
1. Zero Trust Management
BifrostConnect enables your organization to assign a dedicated administrator to define security and access management policies. By emphasizing just-in-time access and granular policy enforcement, BifrostConnect ensures precise access control to specific endpoints and applications.
Access management can seamlessly integrate with your organization’s existing Identity and Access Management (IAM) solution. Additionally, BifrostConnect provides audit logging for tracking usage and monitoring events. These logs can be integrated into your organization’s Security Information and Event Management (SIEM) systems for efficient and streamlined security management.
2. Zero Unit Configuration
Your BifrostConnect solution is dedicated and pre-configured for your organization, allowing Bifrost Units to be shipped directly and installed at the desired location or endpoint. These units provide secure remote access immediately, enabling plug-and-play implementation by nontechnical personnel.
To ensure maximum security, Bifrost Units retain access and security policies even after a hardware reset. Your organization’s security policies are managed exclusively through your dedicated Bifrost Manager, and Bifrost Units cannot be accessed or configured via a local web interface, ensuring the integrity of your BifrostConnect solution.
3. Zero Software Installs
The deployment of the BifrostConnect Solution requires no software installation on endpoints , facilitating a seamless integration process. The user can control where endpoint data is processed, depending on the type of session connection. This flexibility allows for on-premises data processing or data communication between endpoints if permitted.
4. Zero Internet Exposure Bifrost
Units utilize internet connections either in-band or via the integrated out-of-band LTE connection. Crucially, these units do not share the internet connection with the endpoints during a Remote Access Session, ensuring secure and undisturbed communication channels.
5. Zero Network Compromise
Advancing on Zero Trust Network Access (ZTNA) principles, BifrostConnect decouples application access from network access. This reduces your attack surfaces, inhibits lateral movement, and ensures that access to endpoints and applications is exclusively granted to authorized users, eliminating implicit trust.
The solution effectively renders endpoints and network infrastructure invisible to unauthorized users by leveraging inside-out connections from the Bifrost Unit to the user. IP addresses remain hidden from unauthorized users and the internet, ensuring your network remains secure and inaccessible.
Learn more about our security documentation on this page:
BifrostConnect Security Documentation
The World needs another Remote Access solution.
Because the existing ones were not built for commissioning or incident response.
BifrostConnect is not here to replace what already works – it’s here to complement it. PAM, VPN, and RDP are great for steady-state operations. But when systems are offline, isolated, or frozen, they fail.
That’s where BifrostConnect takes over.
Your assurance that no matter the system, site, or situation, you can always connect securely.
It’s the tool you use, when everything else fails.
Why it matters
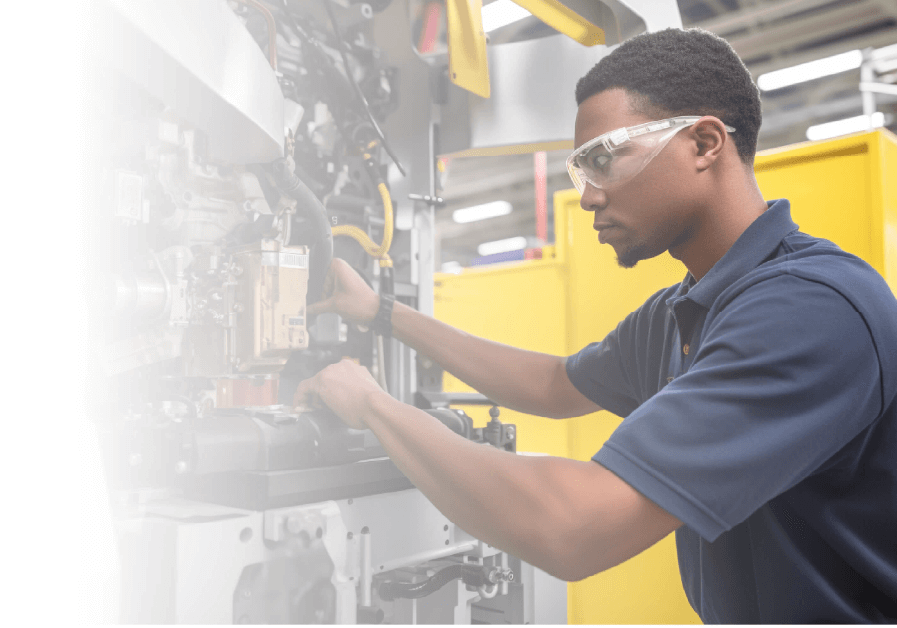
When energy plants, water utilities, or manufacturing lines stall, minutes matter. Traditional IT tools cannot reach assets in commissioning or during outages – leaving experts stranded and downtime escalating.
BifrostConnect closes that gap withthe only solution on the market that seamlessly combines Direct Native Access (native keyboard video, and mouse control) and Direct Tunnel Access (Connect using your native engineering or diagnostic tools) into one unified platform.
We call that ‘Unified Out-of-band Access’, and the result is faster recovery, fewer truck rolls, and proven resilience in critical operations.
The World needs another Remote Access solution.
Because the existing ones were not built for commissioning or incident response.
BifrostConnect is not here to replace what already works – it’s here to complement it. PAM, VPN, and RDP are great for steady-state operations. But when systems are offline, isolated, or frozen, they fail.
That’s where BifrostConnect takes over.
Your assurance that no matter the system, site, or situation, you can always connect securely.
It’s the tool you use, when everything else fails.
Why it matters
When energy plants, water utilities, or manufacturing lines stall, minutes matter. Traditional IT tools cannot reach assets in commissioning or during outages – leaving experts stranded and downtime escalating.
BifrostConnect closes that gap with the only solution on the market that seamlessly combines Direct Native Access (native keyboard video, and mouse control) and Direct Tunnel Access (Connect using your native engineering or diagnostic tools) into one unified platform.
We call that ‘Unified Out-of-band Access’, and the result is faster recovery, fewer truck rolls, and proven resilience in critical operations.
Who We Help
Operations
Ensure business continuity
Cut costs on truck rolls
Streamline commissioning
Maintain uptime with minimal disruption
Enable faster recovery
Cybersecurity & Compliance
Enforce Zero Trust access for both internal and 3rd parties
Provide secure access without backdoors
Maintain security in isolated environments
Generate full audit trails for every OT session
Stay aligned with NIS2 and other compliance requirements
Engineering & Commissioning
Remote access to isolated assets
Support from day one
Commissioning and upgrades
Rapid troubleshooting
Faster incident resolution
Who We Help
Operations
Ensure business continuity
Cut costs on truck rolls
Streamline commissioning
Maintain uptime with minimal disruption
Enable faster recovery
Cybersecurity & Compliance
Enforce Zero Trust access for both internal and 3rd parties
Provide secure access without backdoors
Maintain security in isolated environments
Generate full audit trails for every OT session
Stay aligned with NIS2 and other compliance requirements
Engineering & Commissioning
Remote access to isolated assets
Support from day one
Commissioning and upgrades
Rapid troubleshooting
Faster incident resolution